Product Description
This NIS2 Toolkit is the most comprehensive resource currently available for implementing a cybersecurity compliance programme in accordance with Directive (EU) 2022/2555 (NIS2).
Developed in Microsoft Office format, the documents are fully customisable to address your organisation’s unique requirements. Each template is structured with standard content and includes clearly highlighted example text to guide users in providing the necessary organisation-specific details. Additionally, full example documents are included to support a smooth and effective implementation process.
This toolkit not only simplifies your NIS2 compliance journey but also serves as a vital resource for awareness and training in cybersecurity best practices. Designed for business leaders, compliance professionals, and expert cybersecurity consultants, it provides structured guidance to streamline your path toward NIS2 conformance. Whether you’re seeking to establish a solid cybersecurity governance foundation or strengthen existing controls, this toolkit ensures you have the right resources and support for a seamless compliance process. Enhance Your NIS2 Implementation with Expert Support and Training.
NIS2 Toolkit Author
Authored by a CISSP-certified auditor with over 20 years of experience in Information Security, this NIS2 Toolkit encapsulates decades of expertise and practical knowledge in a user-friendly, ready-to-use format.
This complete NIS2 Compliance Toolkit combines quality and completeness. It provides all the essential documentation required to demonstrate conformance with the NIS2 Directive’s security and reporting obligations. It serves as a robust foundation for compliance and supports the continuous development and improvement of your cybersecurity posture.
Governance Docs have created this pack to comply with Directive (EU) 2022/2555 (NIS2) and its associated technical guidelines, including ENISA recommendations and relevant implementing acts.
What is included in the toolkit?
- 75+ NIS2 Documentation Templates – including policies, procedures, controls, checklists, tools, presentations, and other helpful documentation
- Available as an instant download after purchase
75+ NIS2 Document Templates
NIS2 Cybersecurity Compliance Documentation Pack.
A complete and comprehensive documentation package designed to assist clients, consultants, and service providers in successfully achieving compliance with Directive (EU) 2022/2555 (NIS2).
List of Documents:
-
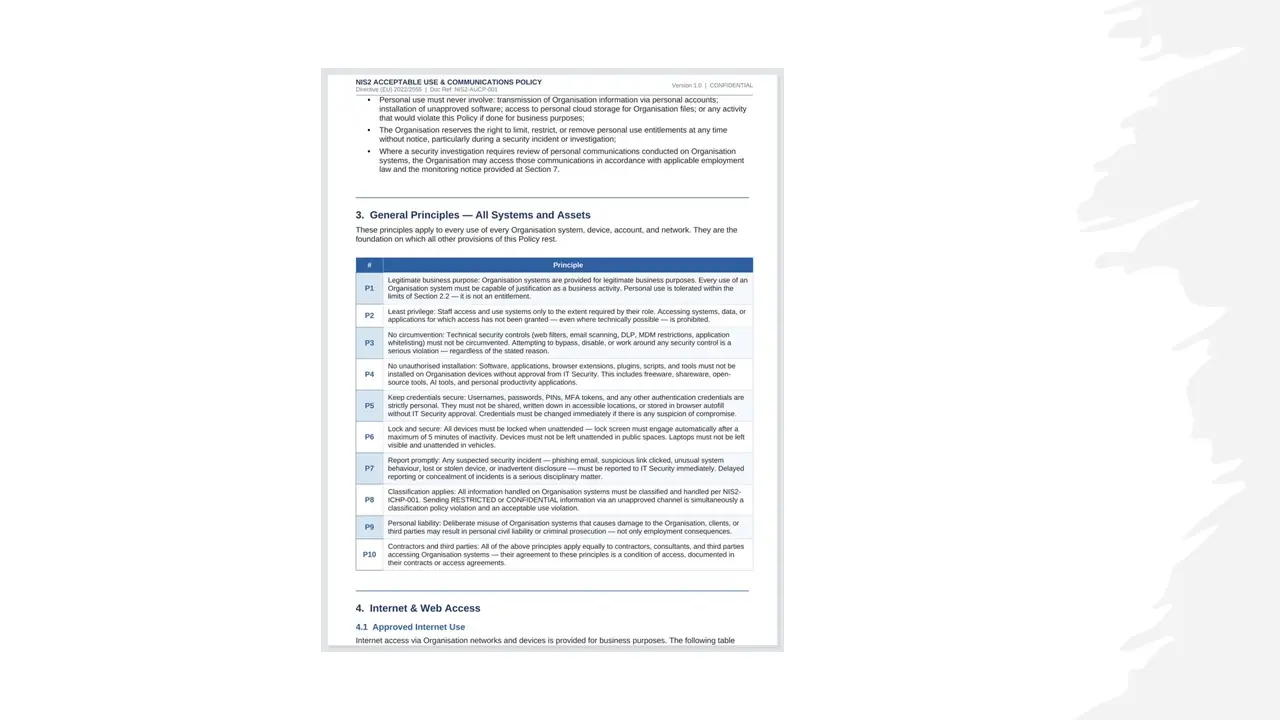
Acceptable Use and Communications Policy.docx
-
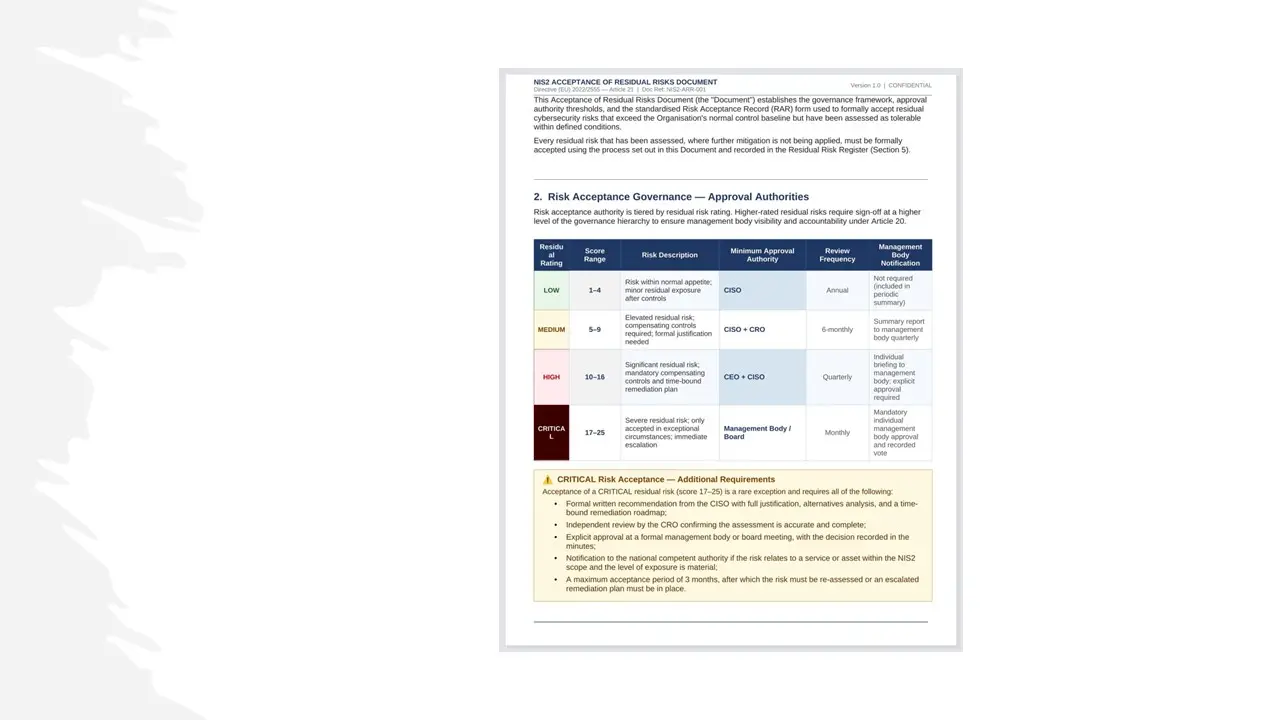
Acceptance of Residual Risks.docx
-
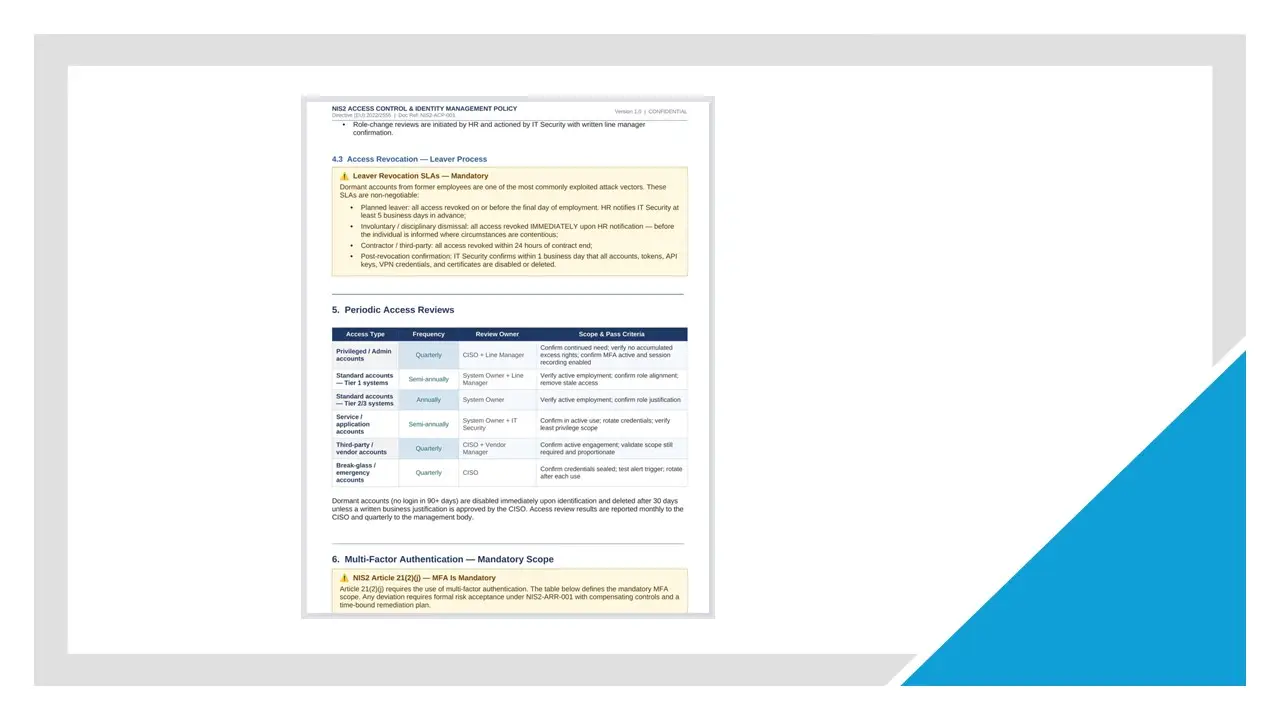
Access Control Identity Management Policy.docx
-
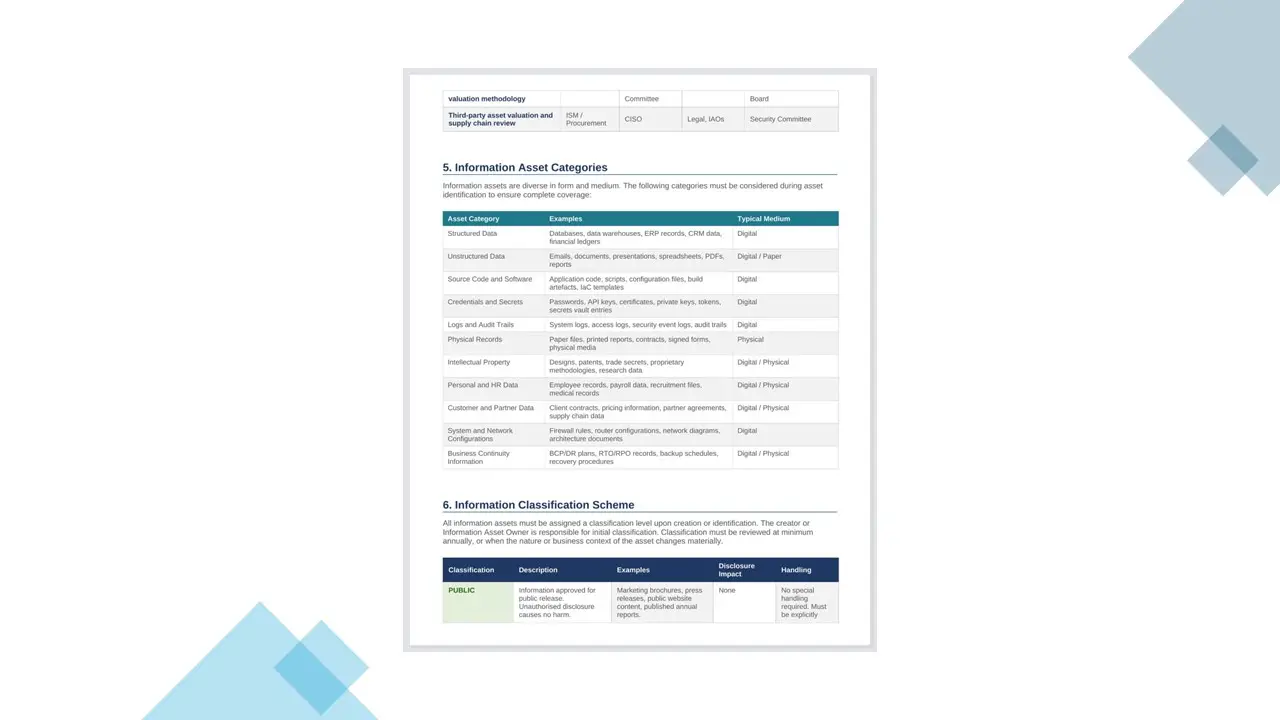
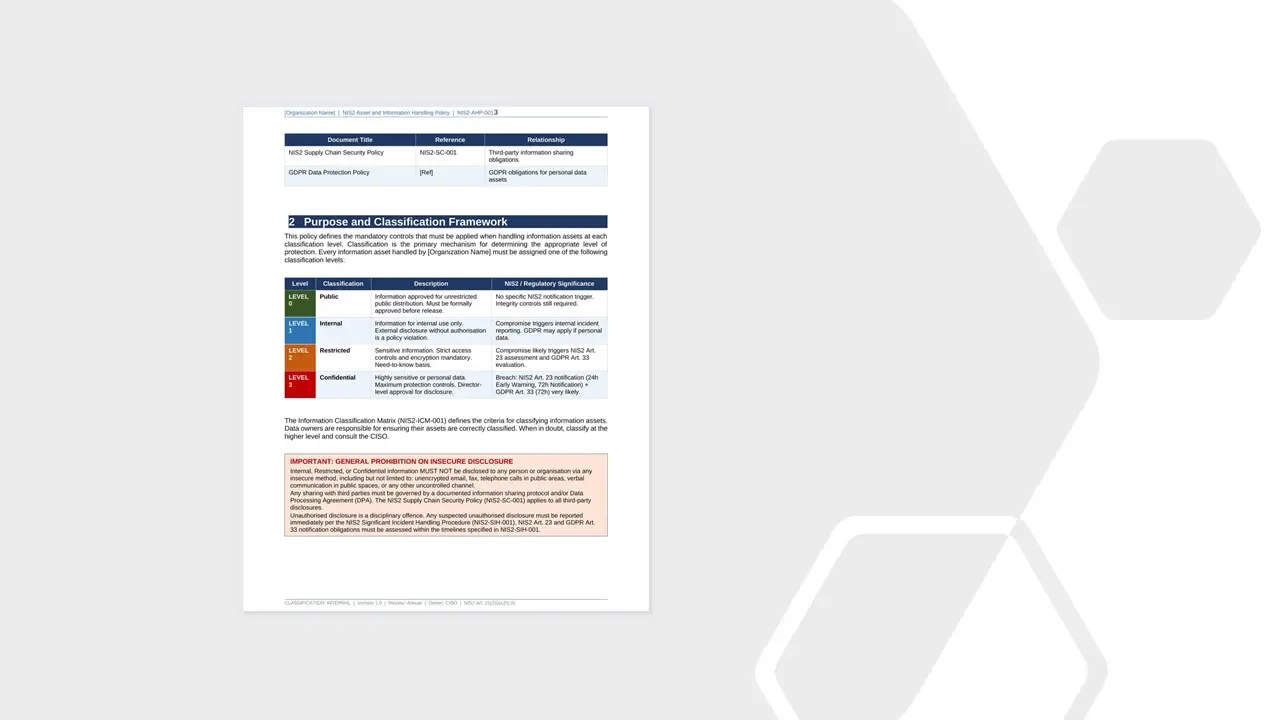
Asset and Information Handling Policy.docx
-
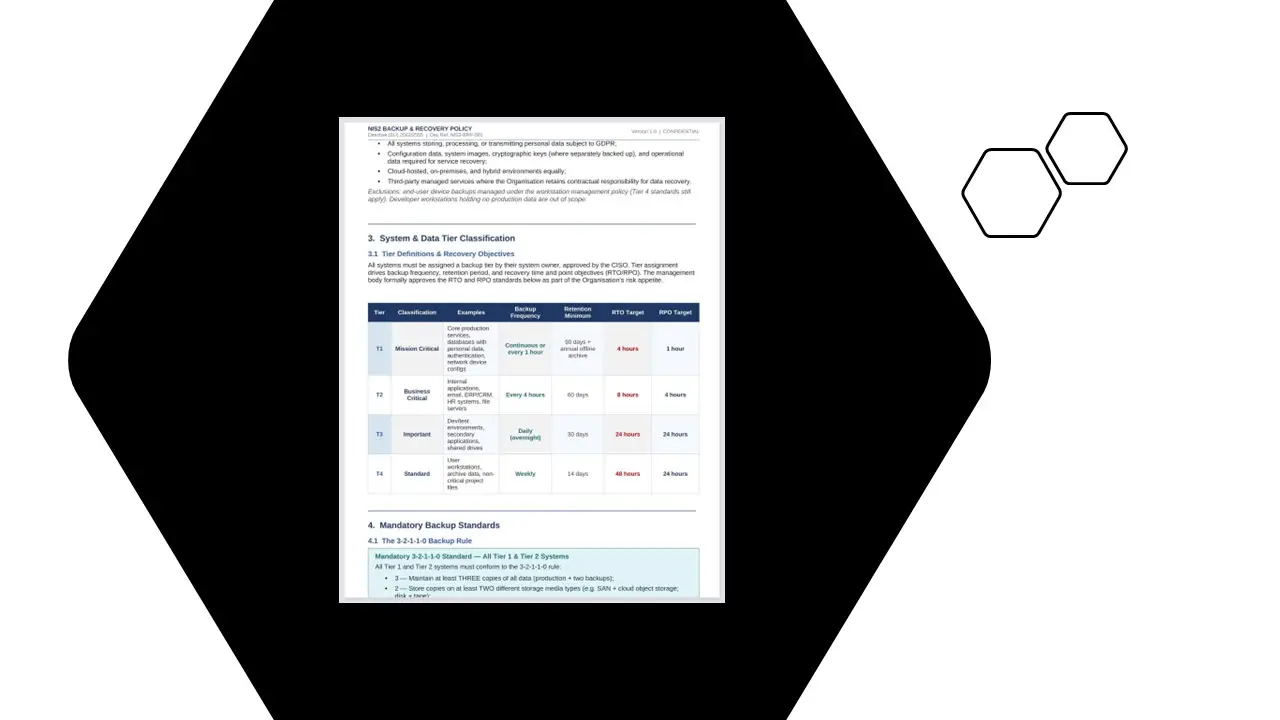
Backup and Recovery Policy.docx
-
BCM Crisis and Operational Resilience Plan.docx
-
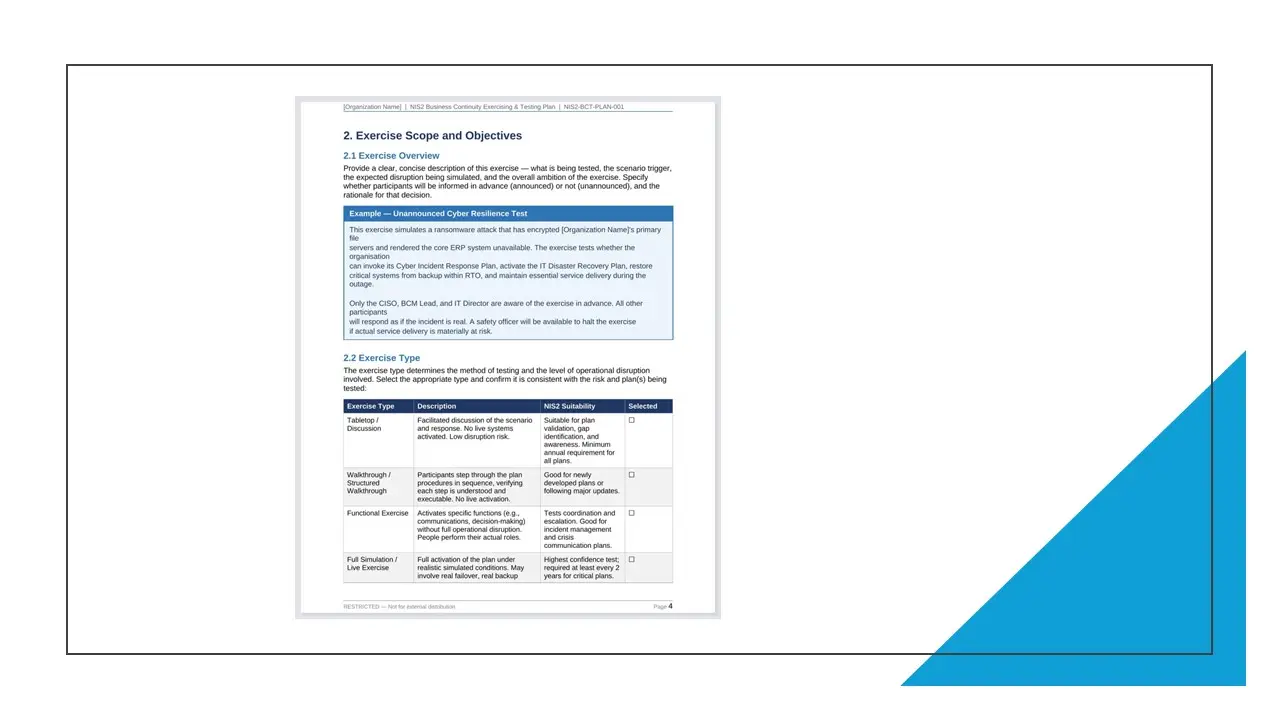
Business Continuity Exercising and Testing Plan.docx
-
Business Continuity Exercising and Testing Report.docx
-
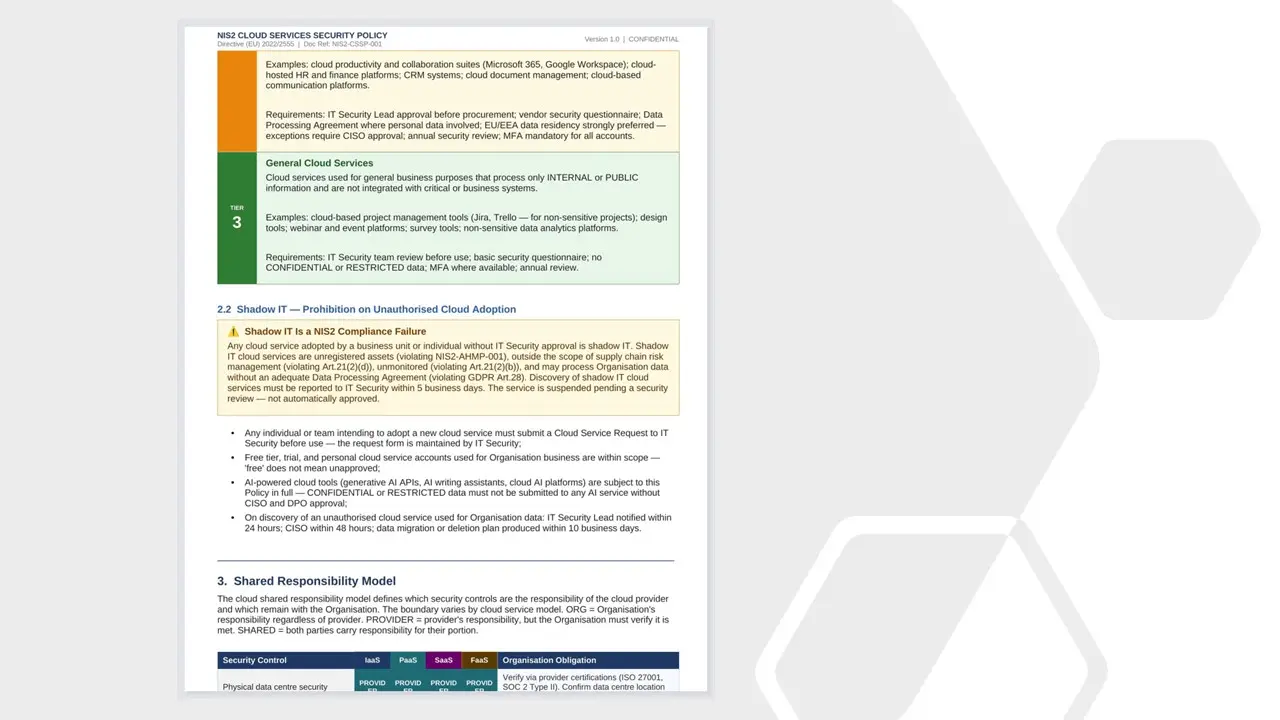
Cloud Services Security Policy.docx
-
Communication Plan.docx
-
Configuration Management Procedure.docx
-
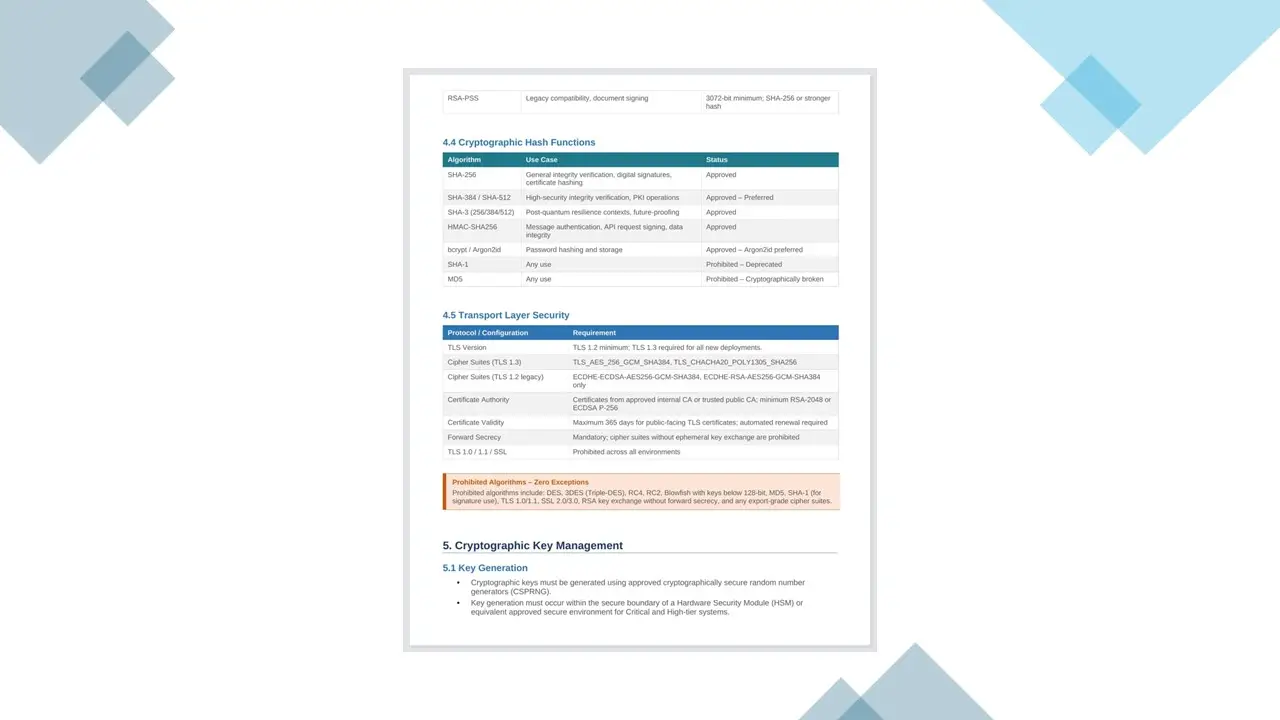
Cryptographic Policy.docx
-
Cybersecurity Control Effectiveness and Improvement Procedure.docx
-
Cybersecurity Governance Management Accountability Policy.docx
-
Cybersecurity Training Records Log.docx
-
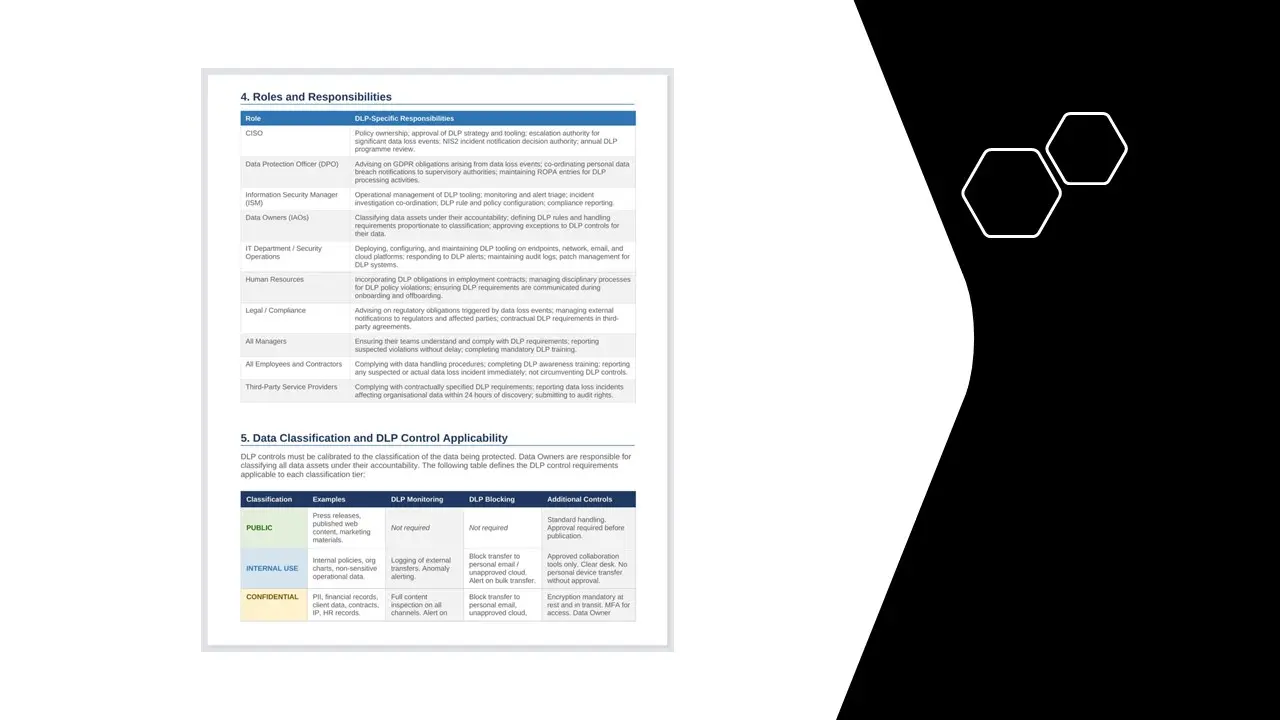
Data Loss Prevention Policy.docx
-
Data Masking Pseudonymisation Policy.docx
-
Data Restoration Form.docx
-
Development Environment Policy.docx
-
Directory of Suppliers and Service Providers.docx
-
Employee Movement and Termination Checklist.docx
-
Employment Contract Cybersecurity Clauses.docx
-
ICT Change Management and Secure Configuration Policy.docx
-
Information Asset Valuation Guideline.docx
-
Information Classification and Handling Policy.docx
-
Information Data Lifecycle Management Policy.docx
-
Information Transfer and Secure Communications Procedure.docx
-
Internal Audit and Compliance Review Procedure.docx
-
Key Contacts Register.docx
-
Legal Regulatory and Compliance Obligations Policy.docx
-
Malware & Cyber Threat Protection Policy.docx
-
Minor Incident Response Procedure.docx
-
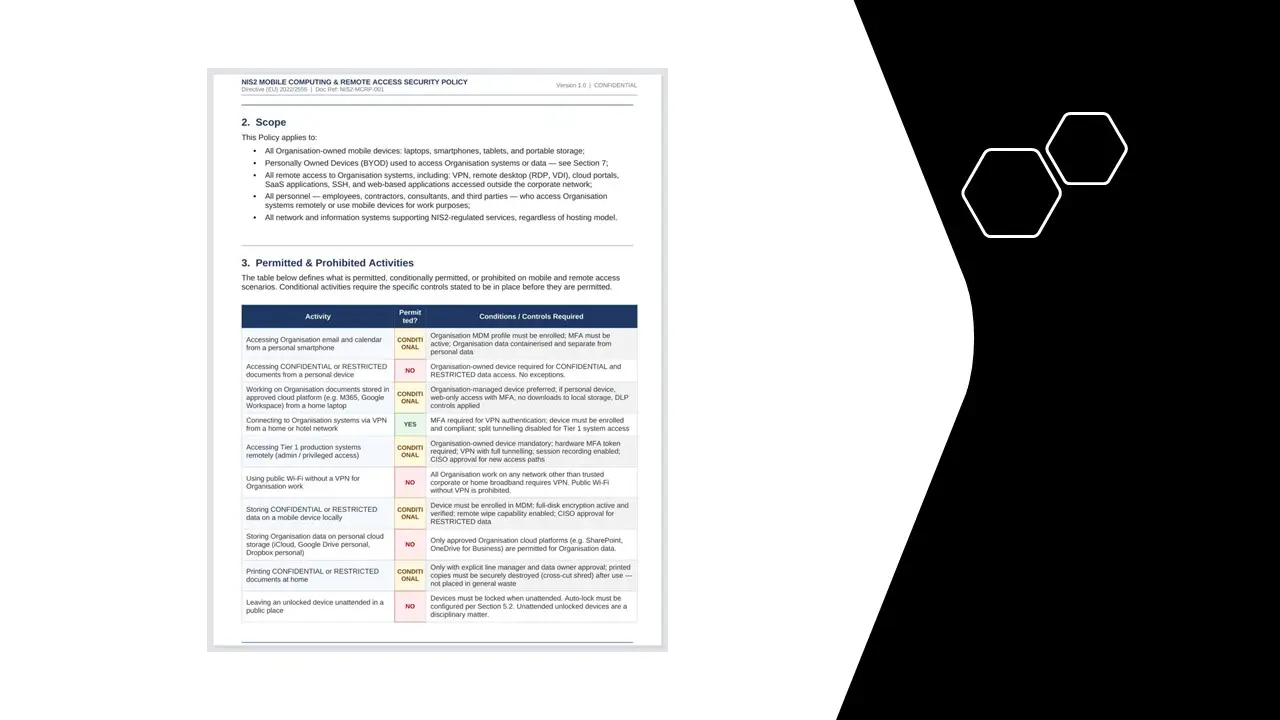
Mobile Computing and Remote Access Policy.docx
-
Network & Information Systems Monitoring Procedure.docx
-
Network Security and Segmentation Policy.docx
-
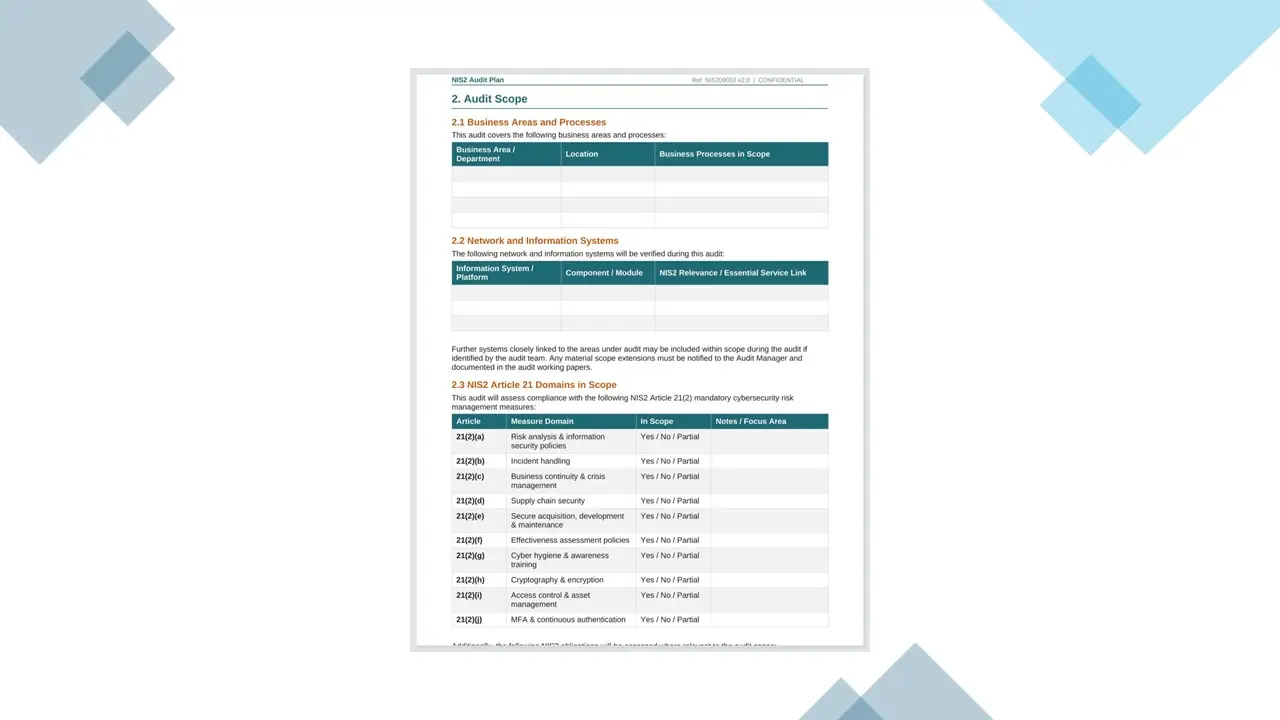
NIS2 Audit Plan.docx
-
NIS2 Audit Schedule.docx
-
NIS2 Audits Procedure.docx
-
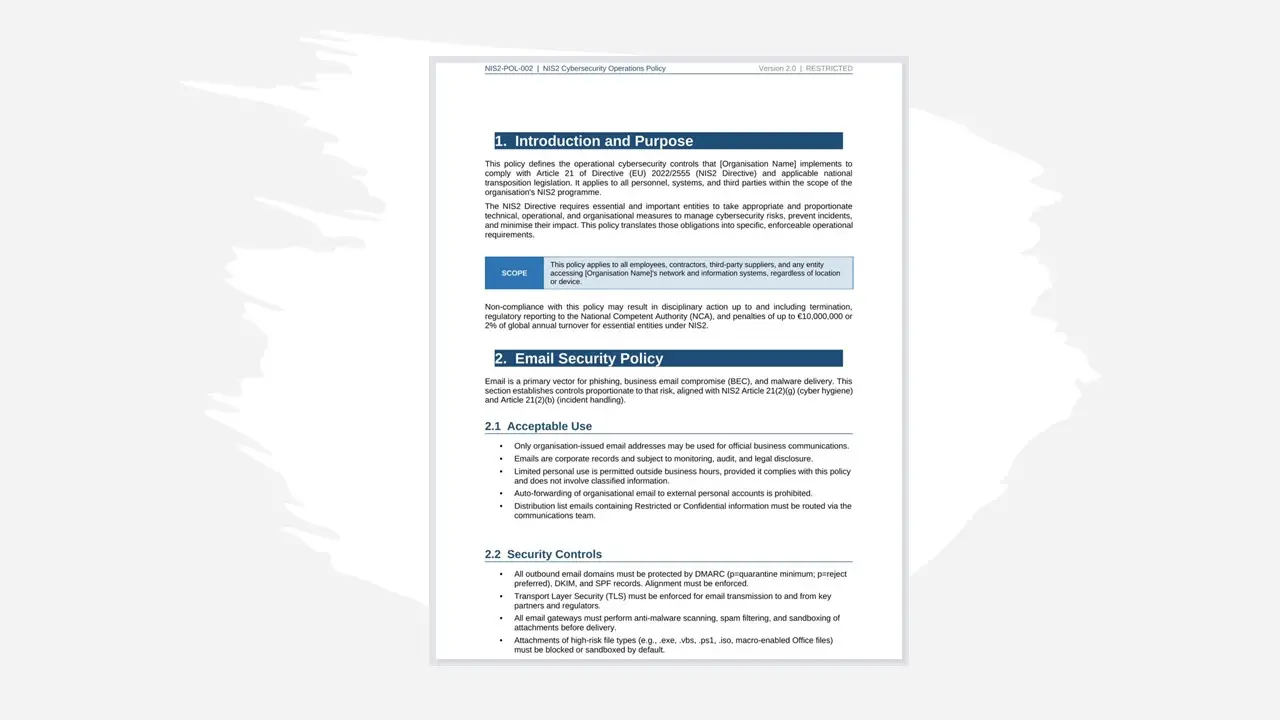
NIS2 Cybersecurity Operations Policy.docx
-
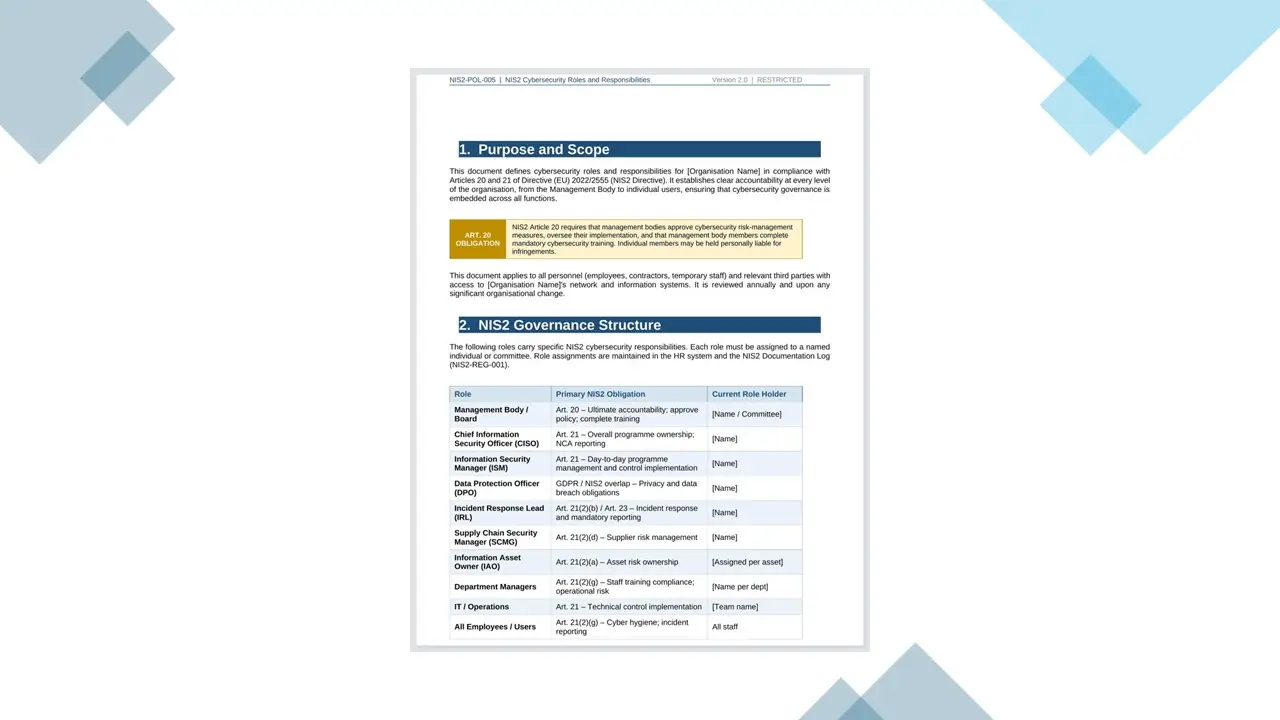
NIS2 Cybersecurity Roles and Responsibilities.docx
-
NIS2 Early Warning Notification Template.docx
-
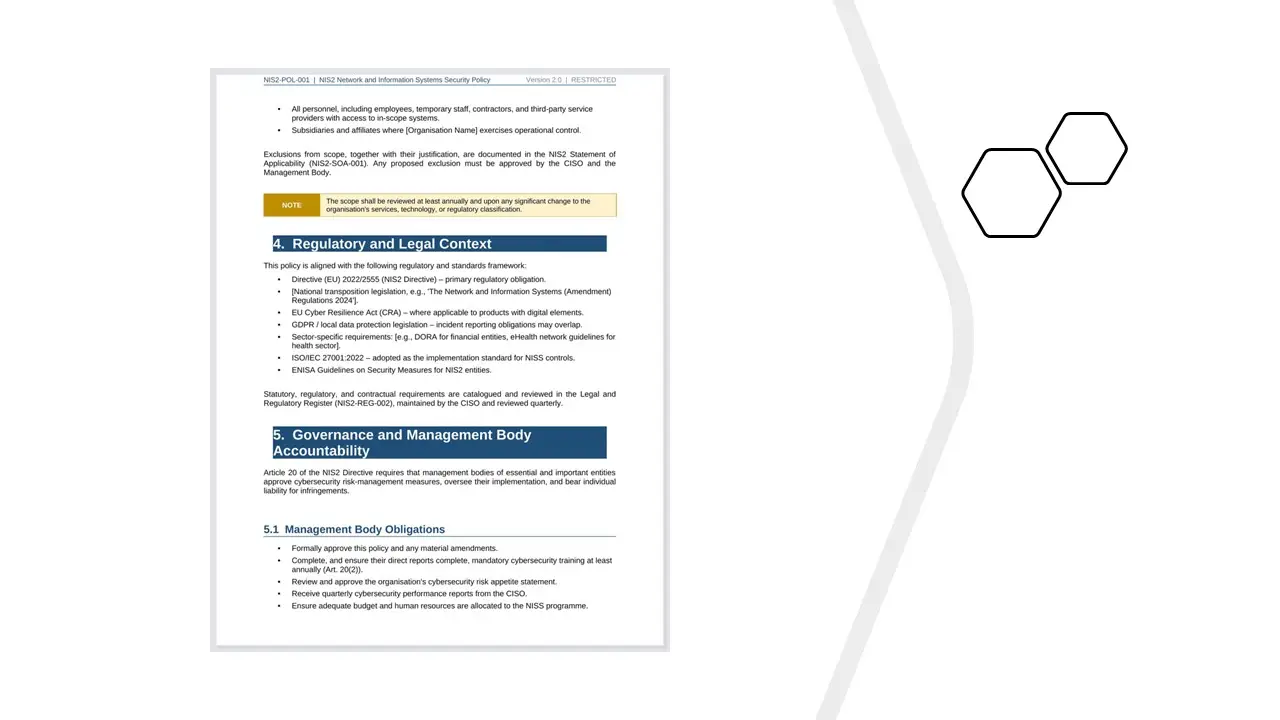
NIS2 Network and Information Systems Security Policy.docx
-
NIS2 Scope and Registration Document.docx
-
Organisation of Information Security.docx
-
Physical Media Transfer Procedure.docx
-
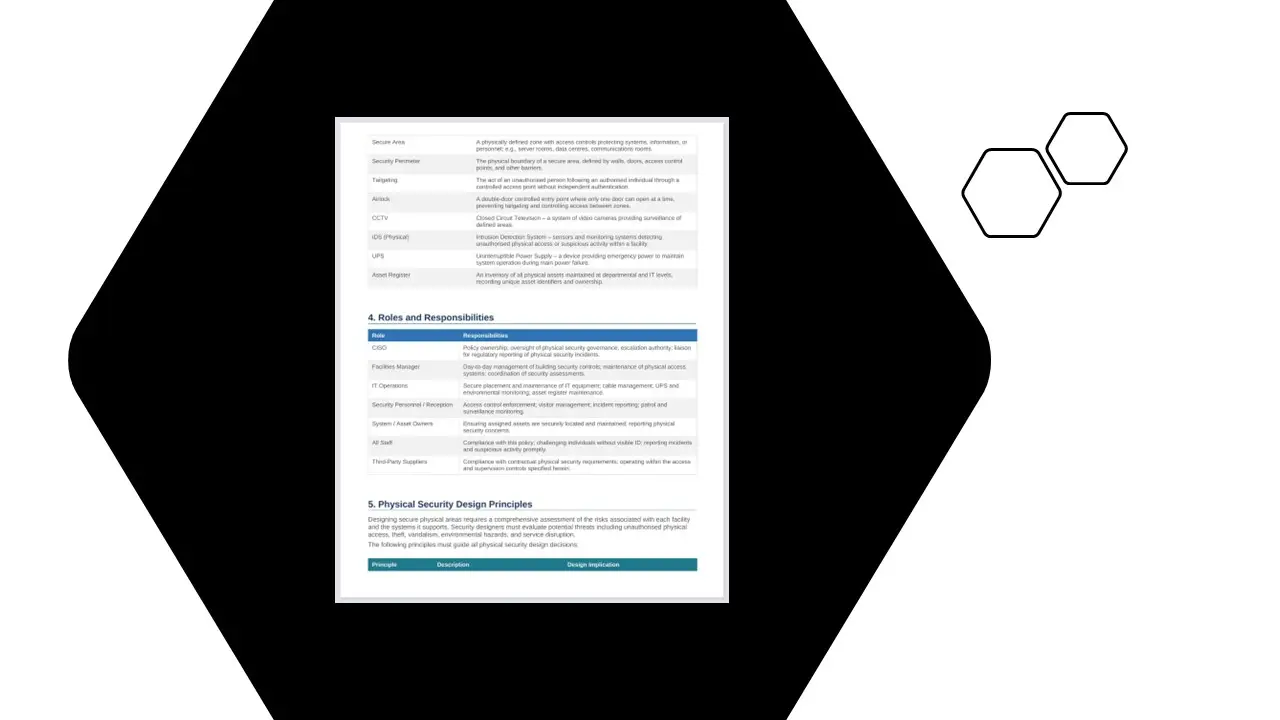
Physical Security Policy and Design Standard.docx
-
Pre-Employment Personnel Security Screening Checklist.docx
-
Project Management Security Policy.docx
-
Recruitment New Joiner Checklist.docx
-
Remote Working Policy.docx
-
Removable Media Management Procedure.docx
-
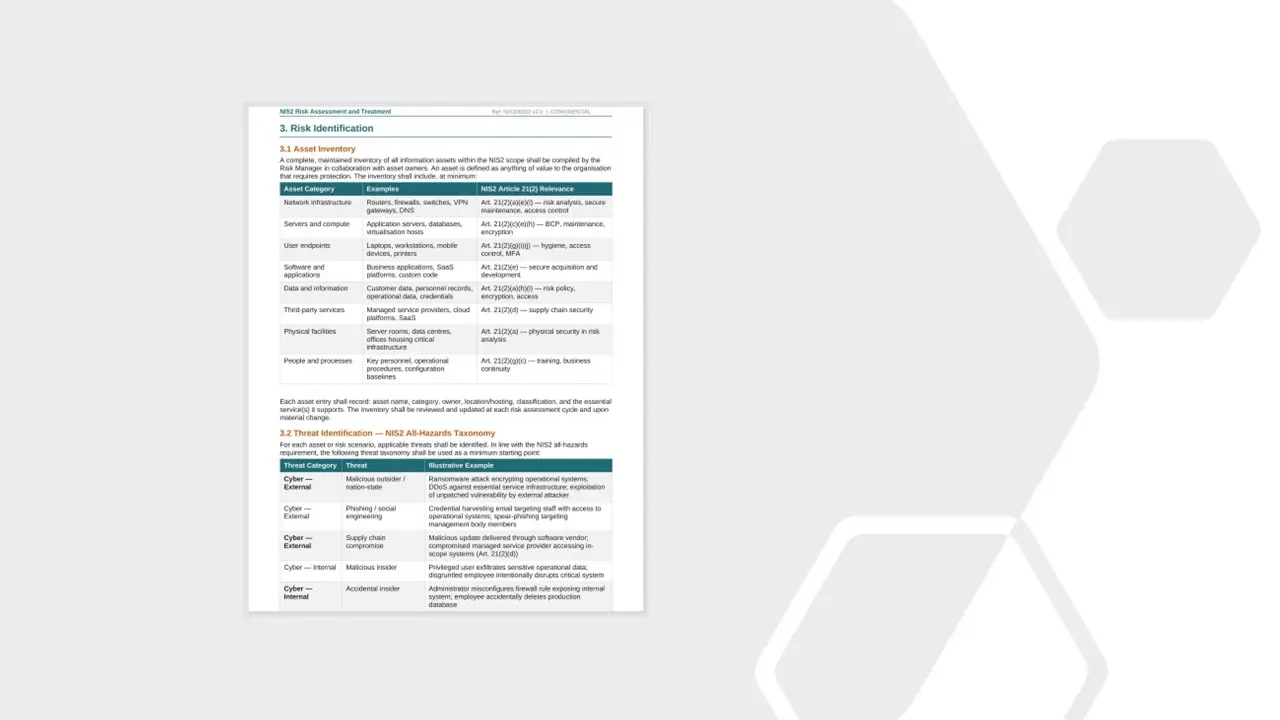
Risk Assessment and Treatment.docx
-
Risk Assessment Report.docx
-
Risk Treatment Plan.docx
-
Secure Areas Policy.docx
-
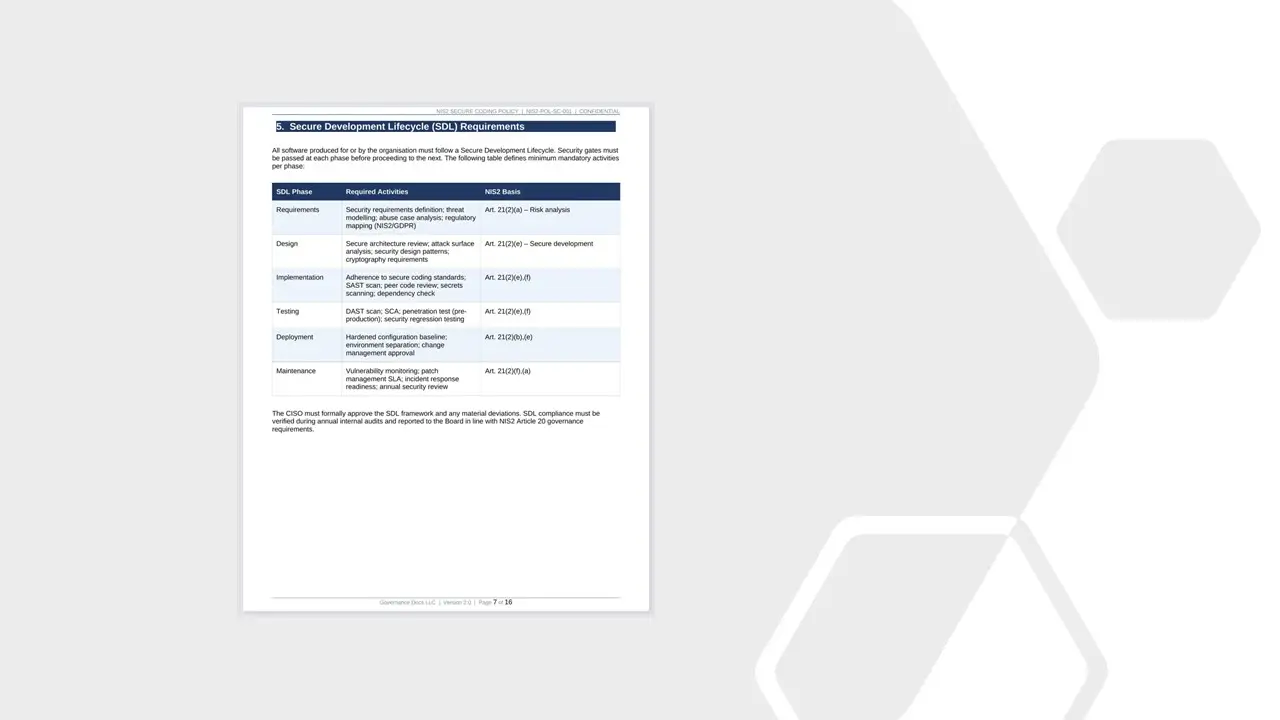
Secure Coding Policy.docx
-
Secure Data Disposal Policy.docx
-
Secure Development and Software Supply Chain Policy.docx
-
Security Event Logging and Monitoring Policy.docx
-
Segregation of Duties Policy.docx
-
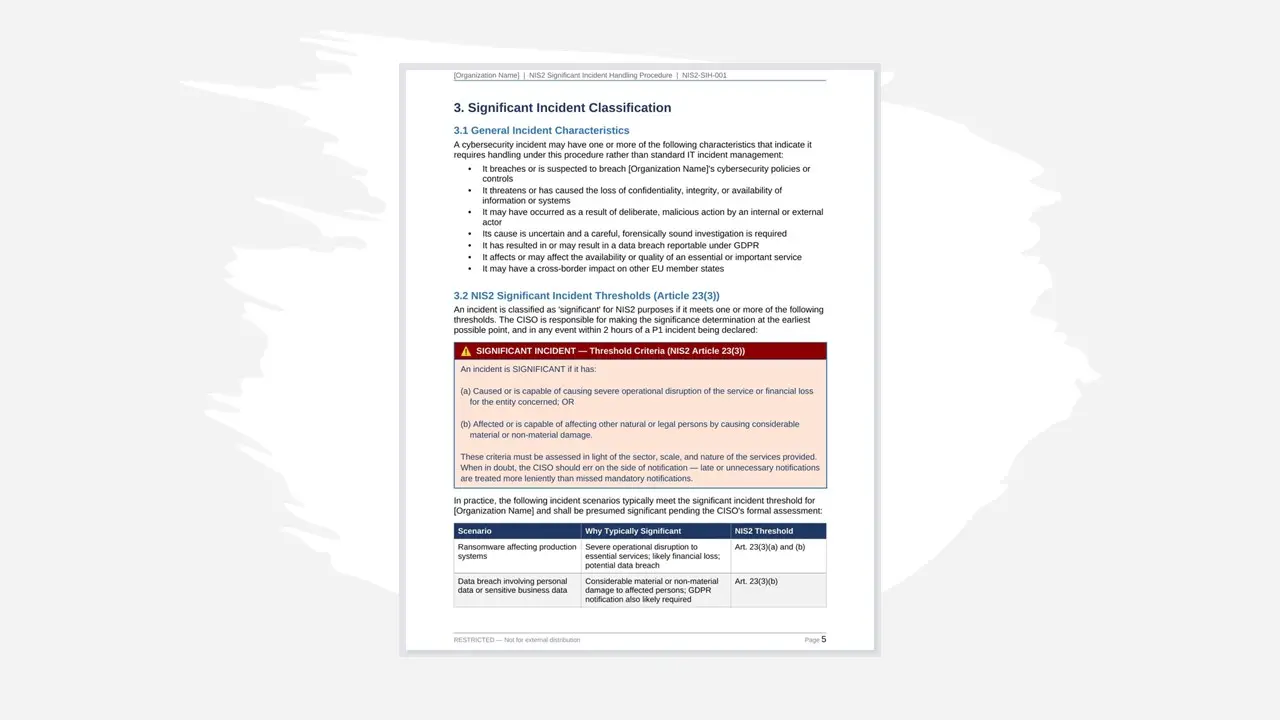
Significant Incident Handling Procedure.docx
-
Significant Incident Reporting Form.docx
-
Stakeholder Email Templates.docx
-
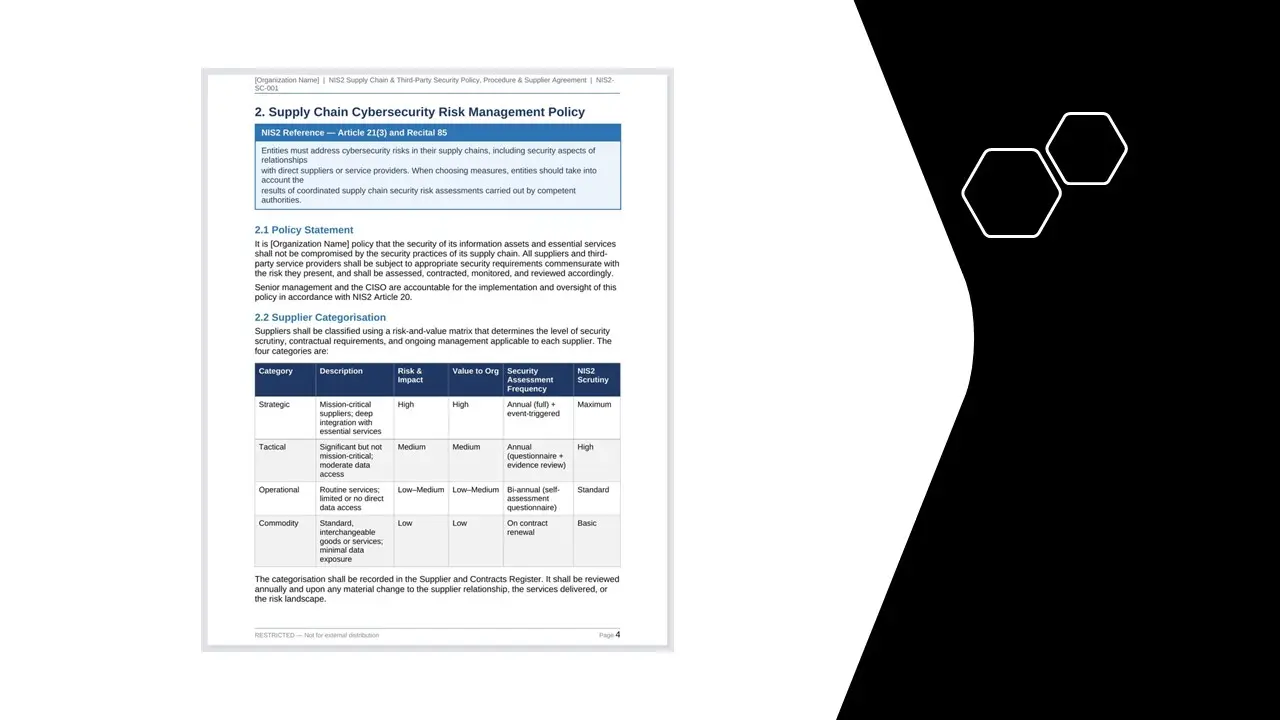
Supply Chain and Third Party Security – Policy_Procedure and Agreement.docx
-
Supply Chain Third Party Risk Assessment Form.docx
-
Technical Briefing on Security Roles and Responsibilities Matrix.docx
-
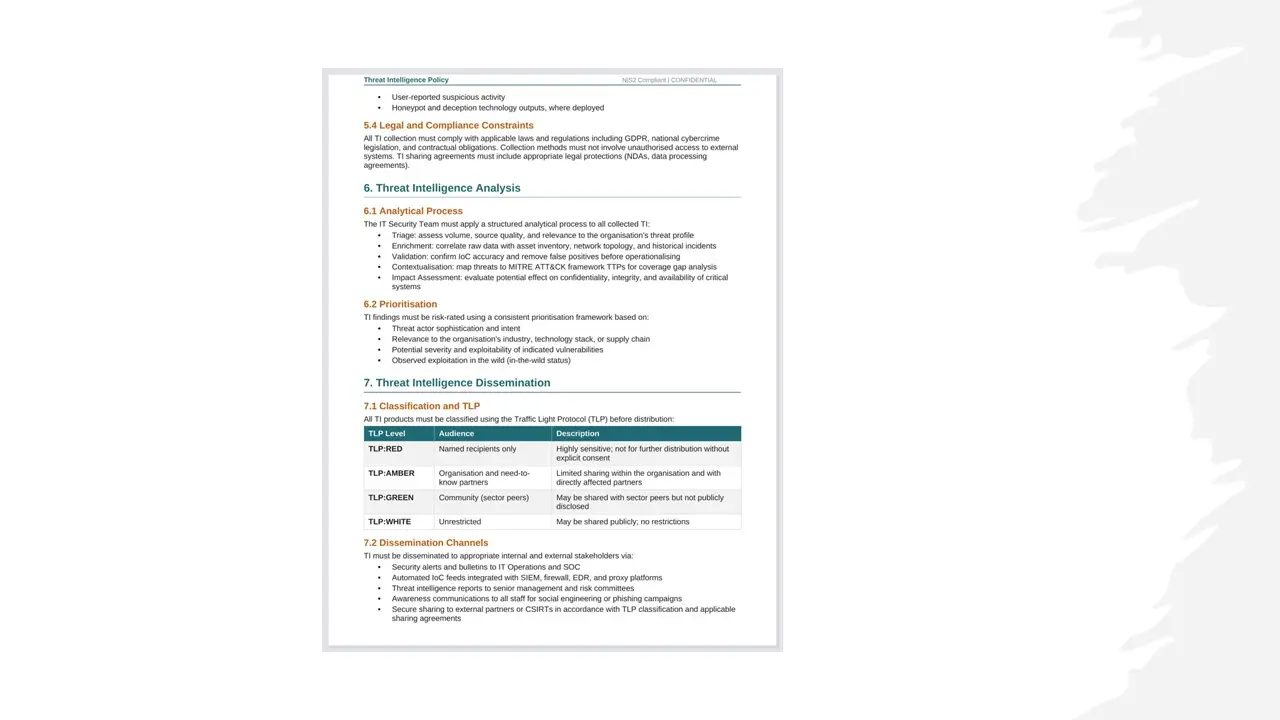
Threat Intelligence Policy.docx
-
Vendor Access Procedure.docx
-
Vulnerability Management Policy and Procedure.docx
-
Web Filtering Policy.docx
-
Asset Register.xlsx
-
Cybersecurity FMEA Workbook.xlsx
-
Information Classification Matrix.xlsx
-
NIS2 Checklist.xlsx
-
NIS2 Information Risk Register.xlsx
-
NIS2 Project Plan.xlsx
-
NIS2 Risk Assessment Worksheet.xlsx
- NIS2 Cybersecurity Awareness Training.pptx
NIS2 Compliance
All documents of this Toolkit are developed based on The NIS 2 Directive
Hence, You just need to download and selected document and add your company name and logo.