Zero-Day Vulnerability Procedure Template
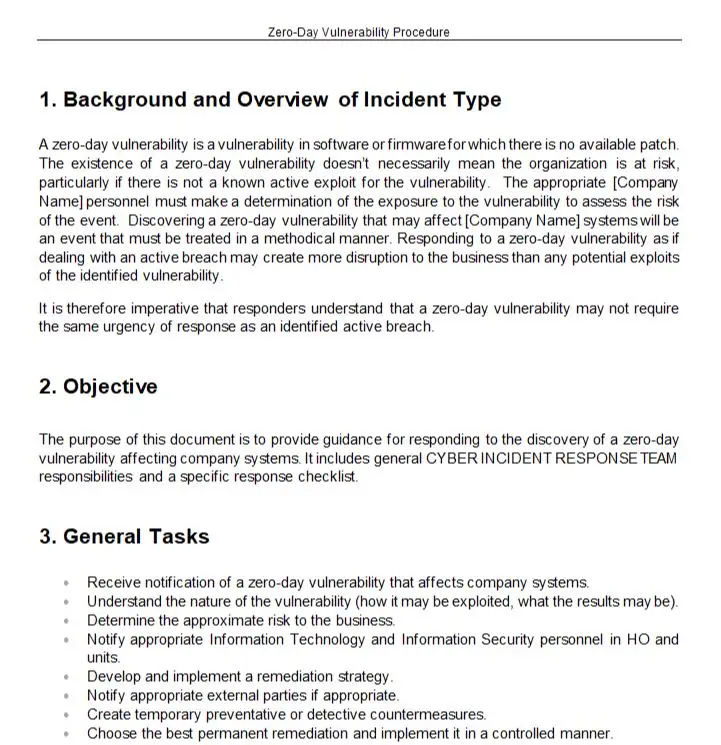
Introducing our Zero-Day Vulnerability Procedure Template, a comprehensive resource designed to assist organizations in effectively detecting, mitigating, and responding to zero-day vulnerabilities—those elusive and previously unknown security flaws that can pose significant risks to your systems and data.
Zero-day vulnerabilities present unique challenges as they are not yet known or addressed by security patches or updates. Our template provides a structured framework to enhance your organization’s preparedness and response capabilities when dealing with these critical security threats.
Key features of our Zero-Day Vulnerability Procedure Template include:
1. Vulnerability Monitoring: Guidelines for actively monitoring reliable sources, security advisories, and threat intelligence feeds to stay informed about emerging zero-day vulnerabilities.
2. Incident Response Planning: A comprehensive approach to incident response planning specific to zero-day vulnerabilities, including roles and responsibilities, escalation paths, and communication channels.
3. Rapid Assessment and Risk Analysis: Step-by-step instructions for quickly assessing the impact and potential risks associated with a zero-day vulnerability, enabling you to prioritize response efforts effectively.
4. Temporary Mitigation Measures: Recommendations for implementing temporary mitigation measures to reduce the exposure to zero-day vulnerabilities while waiting for official patches or vendor solutions.
5. Coordinated Patch Management: Guidance on coordinating with vendors, security researchers, and relevant stakeholders to expedite the release and implementation of patches or workarounds to address zero-day vulnerabilities.
6. Incident Communication and Coordination: Clear communication guidelines for notifying relevant stakeholders, such as IT teams, management, and customers, about the zero-day vulnerability, its potential impact, and the steps taken to mitigate risks.
7. Lessons Learned and Prevention Measures: Encouragement to conduct thorough post-incident reviews to identify lessons learned, enhance incident response processes, and strengthen proactive measures to prevent future zero-day vulnerabilities.
By utilizing our Zero-Day Vulnerability Procedure Template, your organization can improve its readiness and response capabilities when facing these high-risk and time-sensitive security threats. With a clear procedure in place, your team can efficiently detect, assess, and mitigate zero-day vulnerabilities, minimizing the potential impact on your systems and data.
Don’t wait for a zero-day vulnerability to strike. Invest in our Zero-Day Vulnerability Procedure Template today and fortify your organization’s defenses against these elusive and ever-evolving security risks, ensuring the integrity, confidentiality, and availability of your valuable assets.
Number of Pages: 9
A step by step procedure describes the required steps in the case of infection with zero-day vulnerability.
All GovernanaceDocs documents are developed based on well-known standards such as NIST CSF, ISO 27001, ISO 22301, PCI-DSS and HIPAA.
Find More Documents:
Information Security





Our compliance process is now a breeze thanks to these document templates. They’re comprehensive and easy to use.
We’ve recommended these document templates to our business partners, and they’ve all been impressed with the results. These templates have saved us time and helped us maintain a high level of professionalism in our documents.
If you value your time, get these document templates. They’ve made our compliance process so much smoother, and the end results look fantastic. Great job!
Bravo to the creators of these document templates! They’ve made our compliance process so much smoother, and the end results look fantastic. Great job!